OpenID Overview
What Is OpenID?
OpenID is an open, decentralized system for user-centric digital identity. It works on the concept that anyone can identify themselves on the Internet the same way websites do - with a URI (sometimes called a URL or web address, somewhat inaccurately).
Why is OpenID important?
OpenID has emerged as the user-centric identity framework, which allows millions of people to interact online. Beyond authentication, the OpenID framework provides the means for users to share other components of their digital identity. By utilizing the emerging OpenID Attribute Exchange specification, users are able to clearly control what pieces of information can be shared by their Identity Provider, such as their name, address, or phone number.
How Is OpenID implemented in ODS?
ODS supports the OpenID Authentication 1.1 and registration extension 1.0. ODS includes OpenID Server and client side implemented in the weblogs comments using AJAX. When posting a comment, a Web Site url is needed to be entered in order to be verified the authentication against a Server that supports OpenID. The implementation code is located in the openid.js and openid.sql files from the ODS package.
How do I use OpenID?
To see how it works, perform the following steps on our demo server.
- At http://demo.openlinksw.com/ods/ log in as user demo, password demo
- Go to My Weblog.
- Click the "myblog" instance link.
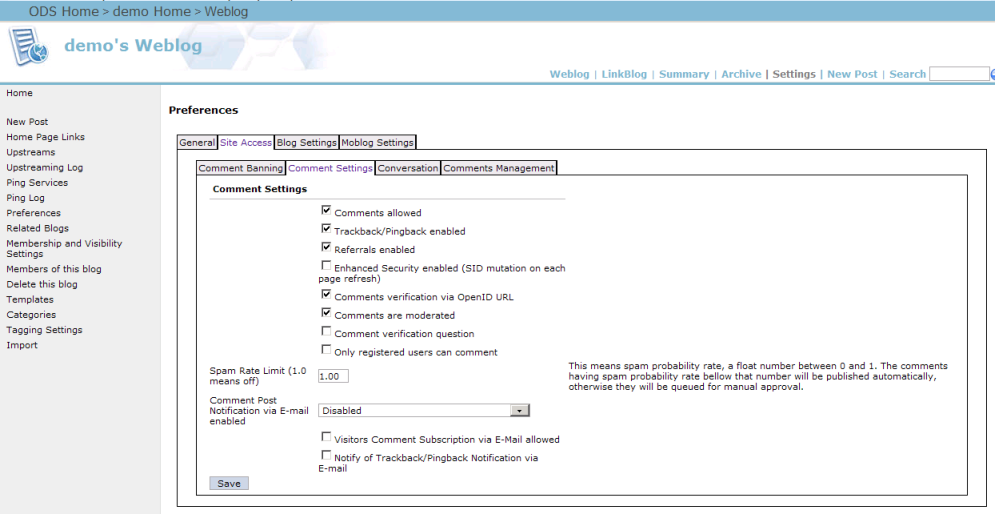
- Go to Settings.
- From the "Preferences" page click the Site Access tab link.
- Click the "Comments Settings" tab link.
- Check the check-boxes for:
- Comments verification via OpenID URL
- Comments are moderated.
- Note: without this check-box checked, the OpenID mechanism will not work correctly.
- Click the "Save" button.
- Click the "New Post" link.
- In the shown form enter:
- For Title: OpenID test
- For Message: This is simple test.
- Click the button "Post"
- Click the link "home" from the left vertical navigation.
- As result will be shown the posted message in step 11.
- Now using different browser access the "myblog" home url: http://demo.openlinksw.com/weblog/demo/index.vspx
- As result will be shown the instance home page with the posted message and the user is not logged in.
- Click the "Comments [0]" link for the post with title "OpenID test".
- As result will be shown the form for posting a comment.
Enter the following:
- For "Name":
test1 - For "Email":
<none> - For "Web Site":
http://myopenlink.net:8890/dataspace/test1>- The value for the "Web Site" field should be a user home page, located at a Server which supports OpenID.
In the given example we can use the myopenlink.net ODS server, which is an OpenID server; user
test1is a registered member of this dataspace. The entered value "http://myopenlink.net:8890/dataspace/test1" is the home page of the user test1.
- The value for the "Web Site" field should be a user home page, located at a Server which supports OpenID.
In the given example we can use the myopenlink.net ODS server, which is an OpenID server; user
- For comment body enter: this is simple comment test.
- For "Name":
- Click the button "Verify".
- As result bellow the "Web Site" field will be shown the following message: Note: You need to grant permission for this site to know who you are. Once you do so, press Login again. and a new window will be opened prompting for credentials at the OpenID Server. In the described case this is myopenlink.net and the page shown is the login page.
- At the login page from step 19.:
- enter for user name test1 and for password 1.
- Click the button "Login".
- As result in front of the "Web Site" field will be shown the icon of the OpenID, which confirms the verification had passed successfully.
- Click the button "Post".
- As result the comment will be post successfully.
- Now open a new window with the same browser you have used in the previous steps, and access the "myblog" home url: http://demo.openlinksw.com/weblog/demo/index.vspx.
- Click the "Comments[n]" link for the "OpenID test" post.
- As result the Web Site value will be "http://myopenlink.net:8890/dataspace/test1", i.e., the cookies keep the url against which verification should be done.
References
Compliant Services
These are services that support OpenID authentication:- WikiTravel
- Zoomr Photo & Geo-tagging Service
- Live Journal
- Wiki Service
- I Make Mistakes Social Networking Service
Compliant Services (Server)
These are services that provide you with an Open ID that can be used at sites supporting OpenID authentication.
- My OpenLink Service
- Claim ID
- Verisign's Personal Identity Provider
- MyOpenID Service
- My ID Service
- Get OpenID Service
Portals
Related
- Power of WebID + OpenID Hybrid Protocol via Internet Explorer & Windows
- Using Safari to Demonstrate WebID + OpenID Hybrid Protocol Power!
- Generate an X.509 Certificate hosted WebID * Safeguarding your Virtuoso-hosted SPARQL Endpoint
- SPARQL Endpoint Protection Methods Collection
- Virtuoso documentation
- Virtuoso Tips and Tricks Collection
- SPARUL over SPARQL using the http://cname:port/sparql-auth endpoint
- Virtuoso Authentication Server UI
- Manage a SPARQL-WebID based Endpoint
- WebID Protocol Support in OpenLink Data Spaces.
- Manage ODS Datadspaces Objects WebID Access Control Lists (ACLs):
- Guide for Set up a X.509 certificate issuer and HTTPS listener and generate ODS user certificates
- Configure Virtuoso+ODS instance as an X.509 Certificate Authority and HTTPS listener
- Configure Virtuoso instance as an X.509 Certificate Authority and HTTPS listener
- Setting up PubSubHub in ODS
- PubSubHubBub Demo Client Example
- Feed subscription via PubSubHub protocol Example
- Setting Up PubSubHub to use WebID Protocol or IP based control lists
- CA Keys Import using Conductor
- Generate an X.509 Certificate (with a WebID watermark) to be managed by host operating system keystore
- Generate an X.509 Certificate (with a WebID watermark) to be managed by a browser-based keystore
- Using Virtuoso's WebID Verification Proxy Service with a WebID-bearing X.509 certificate
- Using Virtuoso's WebID Identity Provider (IdP) Proxy Service with an X.509 certificate
- ODS Briefcase WebID Protocol Share File Guide
- WebID Protocol Specification
- Test WebID Protocol Certificate page
- WebID Protocol Certificate Generation page
